The Hidden Risk of Clinics Without Network Segmentation
A 3-floor private medical clinic with 45 consulting rooms, laboratory, imaging, and emergency services arrived with a flat network where diagnostic imaging equipment (MRI, digital X-rays), patient monitors, medical staff laptops, waiting room WiFi, and the HIS system all shared the same network without separation. A ransomware attack on any administrative computer could potentially reach critical medical equipment.
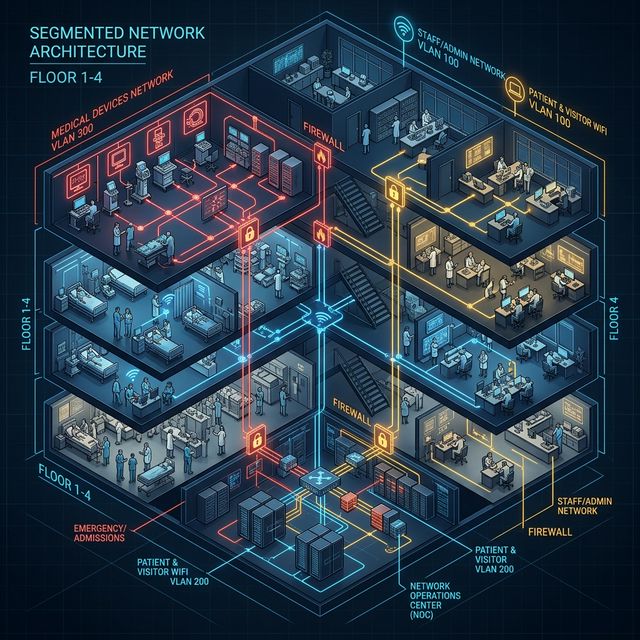
The Secure Medical Network Architecture
- Patient WiFi with Captive Portal: Patients in the waiting room have WiFi on a completely isolated VLAN with a corporate-branded captive portal. They cannot see any internal devices.
- Security Result: In 18 months post-installation, 3 malware attempts detected on reception workstations were completely contained in their VLAN without affecting critical medical systems.
Does your healthcare institution have medical equipment connected on the same network as administrative computers?
We design network architectures for medical institutions with complete isolation of critical systems and privacy standard compliance.
Secure My Medical Network