The Threat That Walks in Silence
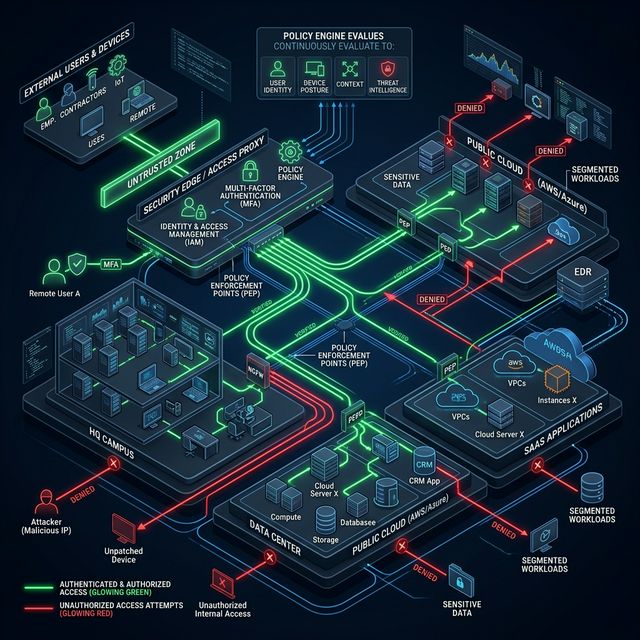
Modern attacks are not instant explosions. They are surgical processes. A sophisticated threat actor can live inside your network for weeks or months before activating a ransomware payload or exfiltrating data. This method — known as "dwell time" — averages 200 days according to Mandiant before detection. By that point, the damage is catastrophic.
Behavioral Analytics: Learning Normal to Detect Abnormal
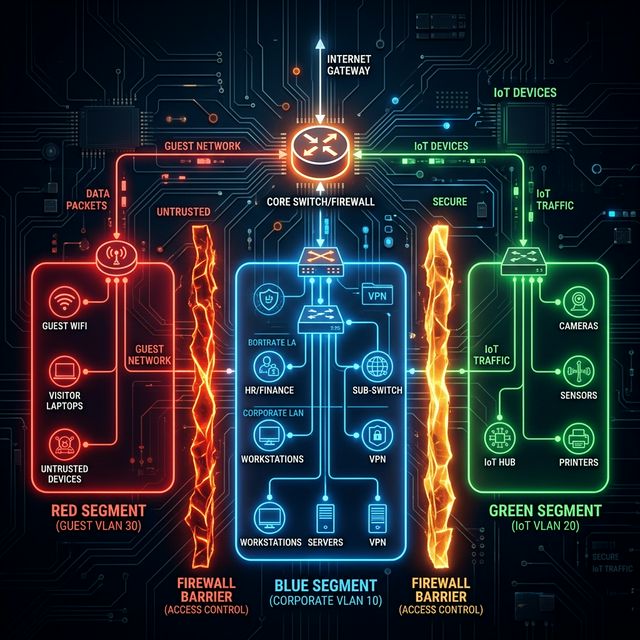
Behavioral anomaly detection establishes a baseline of what is "normal" in your network: which devices communicate, with what frequency, what data volumes they move, and at what hours. Once that baseline is established, any statistically significant deviation triggers an alert.
- NetFlow Inspection: We monitor UniFi router NetFlow logs to analyze communication patterns without needing to decrypt traffic.
- SIEM Integration: Anomaly events feed into a centralized correlation platform that cross-references events from multiple sources to eliminate false positives and prioritize real incidents.
Do you have real visibility into what happens inside your network, or do you only know if the internet is up or down?
We implement network behavior monitoring to detect advanced threats before they explode.
Implement Anomaly Detection