The End of the Trust Perimeter
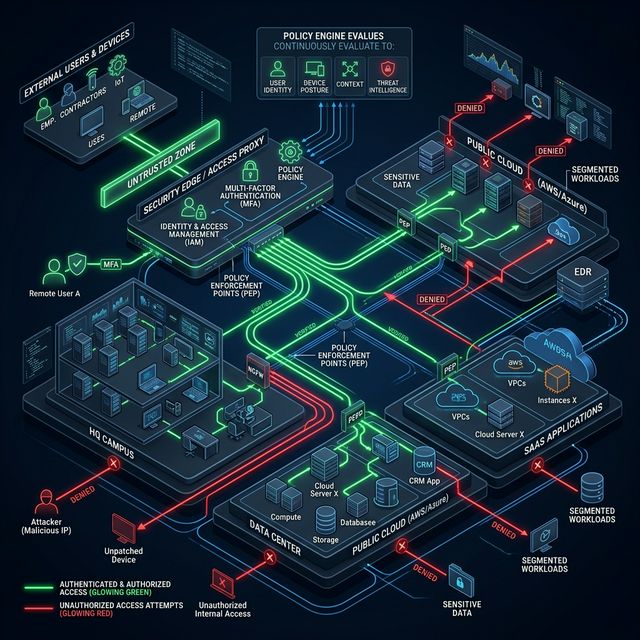
The traditional security model builds a strong wall around the network and blindly trusts everything inside. Zero Trust destroys this concept: no implicit trust zone exists. Every user, every device, every application must authenticate and be explicitly authorized for every resource it attempts to access — no exceptions.
The Three Zero Trust Pillars with UniFi
Pillar 1 — Verified Identity: Every connection requires strong authentication. We implement 802.1X with per-device digital certificates + corporate RADIUS. An unauthorized device physically connected to the switch simply gets no network access, even if it's inside the building.
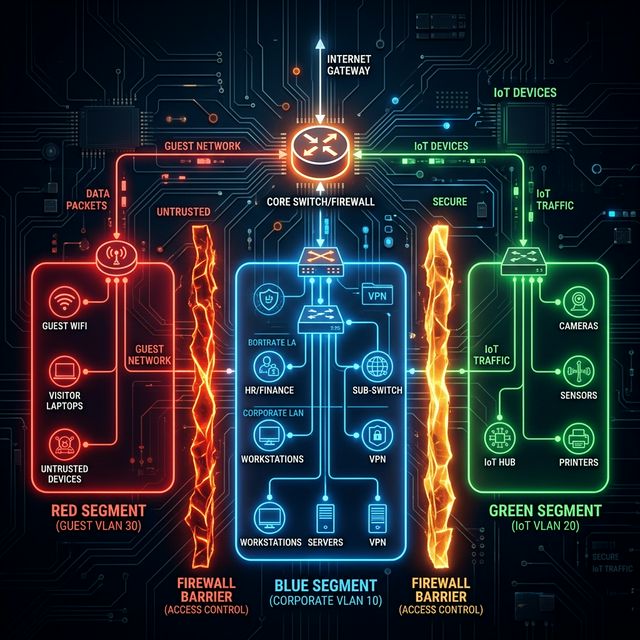
Pillar 2 — Micro-Segmentation: VLANs by business function, not physical location. The HR server can never initiate connections to the Production server even if they're in the same rack. Switch ACLs define exactly what can speak to what.
Pillar 3 — Least Privilege Access: Every user and service receives only the permissions strictly necessary for their function. An accountant cannot — and does not — access development servers. The least privilege principle reduces the blast radius of any compromise.
Can any employee with physical access connect to any part of your network without restrictions?
That's the most underestimated internal risk. We design and implement Zero Trust architecture on your existing UniFi infrastructure.
Implement Zero Trust